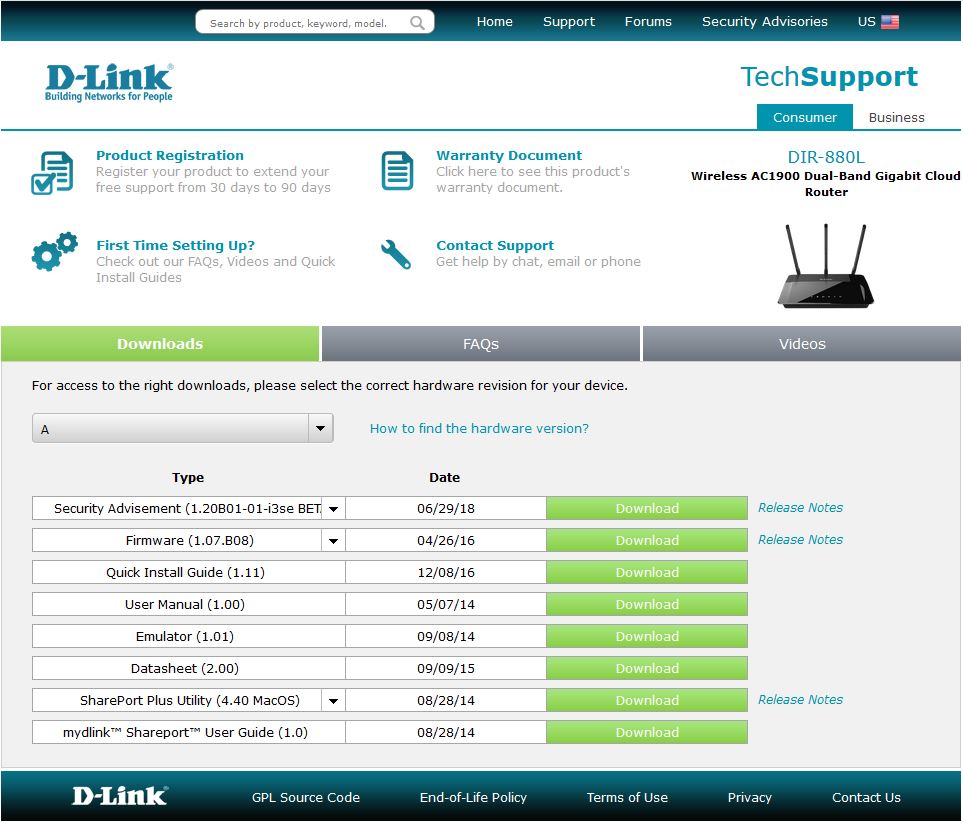
It is time to upgrade router firmware.
There is a alert notice on the support.dlink.ca
Security Advisory: New firmware has been released that fixes the latest HNAP Privilege Escalation Vulnerability. Please ensure to upgrade your router to the latest firmware version. Click on on the Downloads tab below.
What kind of vulnerability this time?
Here is a detailed information page about it. http://www.dlink.com/uk/en/support/support-news/2015/april/13/hnap-privilege-escalation-command-injection
An attacker who wishes to gain access to the router sends an unprivileged HNAP command such as GetDeviceSettings, they append to the command an additional command separated with an “/”, which is used as a separator between commands. Any command(s) after the first will be executed unauthenticated. Additionally, additional commands will be passed directly to the underlying Linux system, allowing the injection of arbitrary system commands.
The GetDeviceSettings HNAP Command is used to indicate some very common parameters (e.g. the domain name of the HNAP device), as well as to define which HNAP commands are available.
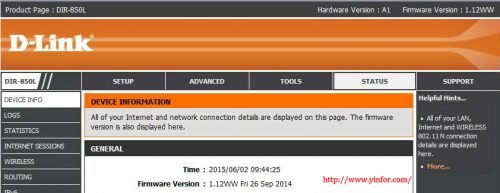
Before upgrade, it is v1.12WW
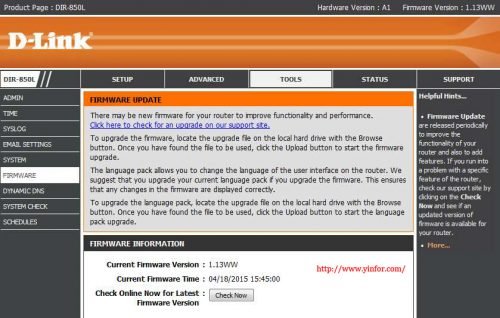
After upgrade, it is v1.13WW
Download link of v1.13 firmware for A1 hardware.
ftp://ftp.dlink.ca/PRODUCTS/DIR-850L/DIR-850L_REVA_FIRMWARE_1.13.BIN
How to upgrde firmware?






TYVM.