
No more space of my Web Server
This afternoon, I found my site was not accessible when I tried it. So I went to the Webmin panel. It loaded, but with a warning, disk space is running out. It is kind of urgent. All websites on this...
Tech geek. Life geek.

This afternoon, I found my site was not accessible when I tried it. So I went to the Webmin panel. It loaded, but with a warning, disk space is running out. It is kind of urgent. All websites on this...

This is my blog’s new UI. It is new, so I hope it is suitable for all my audience needs. It is based on the UNOS publisher theme. I would like to recommend you to use this professional WordPress theme....
I checked my Nginx log files and saw a lot of errors as below: *11047 FastCGI sent in stderr: “PHP message: PHP Warning: Parameter 1 to W3_Plugin_TotalCache::ob_callback() expected to be a reference, value given in /home/users/yinfor.com/wp-includes/functions.php on line 3597” while...
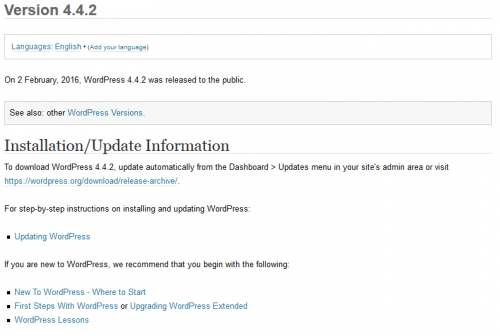
It is a security update. Some of my Blogs do not have auto-update. So, manually update it by sign in.
It is time to upgrade my WordPress installation to 4.4.
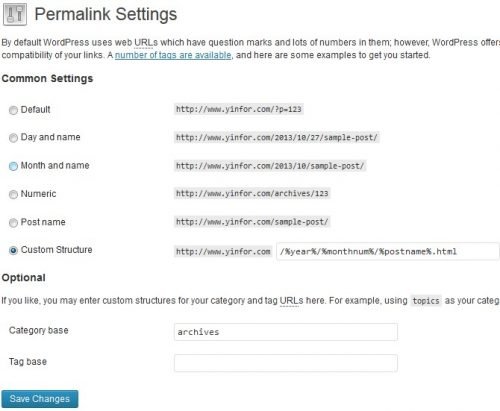
There are very few guide on web about migrate blog from MovableType 5.27 to WordPress 3.7. Here is my own experience to do it. Step 1: Prepare the data on MovableType 5.27 Using MovableType export function is not enough, because...

It is a hard decision. When you saw this post, this blog is moved to new VPS. It is changed from MovableType to WordPress. First of all. I like changes. Changes make us better. It took me about two days...

It is time to upgrade WordPress to the latest 3.5.1. It is a maintenance and security update. From the announcement post, this maintenance release addresses 37 bugs with version 3.5, including: Editor: Prevent certain HTML elements from being unexpectedly removed...

WordPress 3.4.2 released today. I did a quick upgrade on my WordPress installations. It is a security update, so, do not wait. Fix some issues with older browsers in the administration area. Fix an issue where a theme may not...
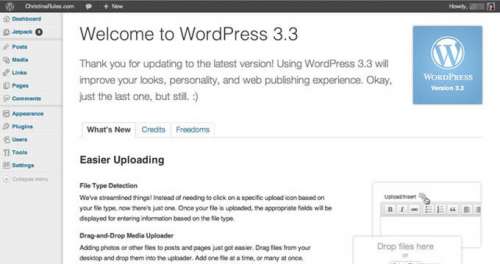
I upgraded almost eight blogs powered by WordPress yesterday when I got the release news of WordPress 3.3.1. WordPress 3.3.1 is now available. This maintenance release fixes 15 issues with WordPress 3.3, as well as a fix for a cross-site...

During past week, I saw two shell accounts are hacked. Both are on Dreamhost. One of it is reported by Google Webmaster Tools. It said there are some malicious code found. The other one is found, because that the memory...

Just few days after the release of WordPress 3.2, wordpress 3.2.1 released. It is said that it fixes a JSON-related server incompatibility problem that affected some users. Fixes for the new dashboard design and the Twenty Eleven theme, based on...

Just noticed that WordPress 3.2 released few days ago. There are some new features and improvement on UI and others. The most important parts I like are the big changes of it. 1) No more IE6. Actually, there is no...

WordPress v3.1 is released yesterday. I upgrade four blogs powered by WordPress from 3.05 to 3.1. What’s New in WordPress 3.1 According to the WordPress Codex, there are a lot of new features to be found, however, here is a...

WordPress 3.0.5 is released and has following bugs fixed. Summary * Fix XSS bug: Properly encode title used in Quick/Bulk Edit, and offer additional sanitization to various fields. Affects users of the Author or Contributor role. (r17397, r17406, r17412) *...