The newly added user’s password is not saved in Ubuntu 22.04lts. Only the password hash is stored in /etc/shadow.
Here is an example:
userabc:$y$j9T$UPMI.SI5JREVmHrdU0eLb.$ypKG.QfSXqxIJLVLzrMm20E7Ub.arrTYRBhveJshzv0:19824::::::
The string is separated by colon symbols.
The user name is: userabc
The whole password part is: $y$j9T$UPMI.SI5JREVmHrdU0eLb.$ypKG.QfSXqxIJLVLzrMm20E7Ub.arrTYRBhveJshzv0
$y$j9T$UPMI.SI5JREVmHrdU0eLb.$ is the algorithm prefix and salt.
ypKG.QfSXqxIJLVLzrMm20E7Ub.arrTYRBhveJshzv0 is the hash.
19824 is the last password changed(lastchanged). It is expressed as the number of days since Jan 1, 1970 (Unix time). Here 19824 means April 11, 2024.
Then there are 5 empty strings between colons. They stand for following.
Minimum: The minimum number of days required between password changes.
Maximum: The maximum number of days the password is valid, after that user is forced to change her password again.
Warn: The number of days before the password is going to expire that the user is warned that his password must be changed.
Inactive: The number of days after password expires that account is disabled.
Expire: The date of expiration of the account, expressed as the number of days since Jan 1, 1970.
Let’s get back to the password itself.
$y$j9T$UPMI.SI5JREVmHrdU0eLb.$ypKG.QfSXqxIJLVLzrMm20E7Ub.arrTYRBhveJshzv0
$y$ is yescrypt.
There are also some old algorithm.
$1$ is MD5
$2a$ is Blowfish
$2y$ is Blowfish
$5$ is SHA-256
$6$ is SHA-512
The latest one, the default of Ubuntu 22.04 is yescrypt.
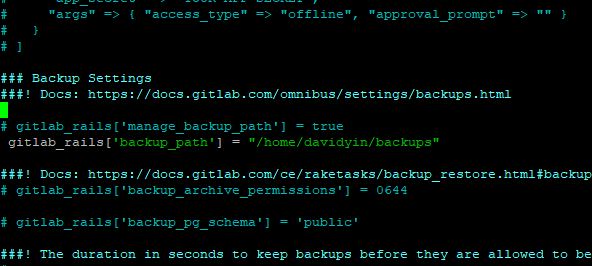
Here is a way to verify the password with the hash.
It uses Perl’s crypt() function.
$ export PASS=password SALT='$y$j9T$F31F/jItUvvjOv6IBFNea/$'
$ perl -le 'print crypt($ENV{PASS}, $ENV{SALT})'
$y$j9T$F31F/jItUvvjOv6IBFNea/$pCTLzX1nL7rq52IXxWmYiJwii4RJAGDJwZl/LHgM/UD
It gives you a chance to double-check the password and the hash with the salt.
Reference:
Ubuntu Features.
Password hashing
The system password used for logging into Ubuntu is stored in /etc/shadow. Very old style password hashes were based on DES and visible in /etc/passwd. Modern Linux has long since moved to /etc/shadow, and for some time now has used salted MD5-based hashes for password verification (crypt id 1). Since MD5 is considered “broken” for some uses and as computational power available to perform brute-forcing of MD5 increases, Ubuntu 8.10 and later proactively moved to using salted SHA-512 based password hashes (crypt id 6), which are orders of magnitude more difficult to brute-force. Ubuntu 22.04 LTS and later then moved to yescrypt to provide increased protection against offline password cracking. See the crypt manpage for additional details.