Cyberattacks are, in some ways, an invisible and unpredictable threat, but they can have awful consequences for businesses of all sizes. Around a quarter of businesses will fall victim to a cyberattack, so it is important to prepare for the worst. The best way to eliminate threats to your network is to be proactive and understand the threats you are up against, but with cybercriminals changing their tactics all the time, this is easier said than done. To get you started, here are some tips and techniques you may want to consider when establishing a strong perimeter around your network.
Adopt a Zero Trust approach
The standard approach to perimeter network security is to concentrate on preventing unauthorised users from accessing the network (through firewalls, VPNs, multi-factor authentication, etc.). However, this does not protect the network from users within the network, and many hackers have ways of getting past these defences. A user only needs to find out the relevant passwords, and they would be able to access a network.
A Zero Trust approach to security makes the user prove that they are not attacking the system, even in they are already working within the perimeter. With Zero Trust, you can also limit what a user can access even when they have passed the perimeter. Find out more about what is zero trust security now.
Improve the physical security of your premises
Your premises should be secure for many reasons, but if you have your network onsite, you have another reason to prevent intruders from crossing the boundary. Options include alarms, lighting, security guards, digital locks, and much more. Ten ways to protect your business from crime.
Train your employees regularly
You, your management team, and employees should be trained in cybersecurity risks as well as how to prevent and deal with cyberattacks. This should include your network administrators who will have responsibility for managing security on a day to day basis. New technologies are being developed all the time to combat the new techniques used by cybercriminals. When employees are aware of the risks posed by phishing emails, clicking on suspicious downloads, or divulging sensitive information to unknown people, the likelihood of human error is significantly reduced. This training should be repeated regularly to ensure they are aware of the latest cyberattack tactics.
Strengthen your authentication procedures
Passwords are often weak, and a lot of people will use the same password for all their accounts or stick with default passwords. You should ensure that your staff are using different passwords for different systems, that passwords are changed regularly, not recorded anywhere unauthorised people could find them, that they are complex, and not related to personal information. Ideally, you should incorporate multilevel authentication to bring in extra layers of security.
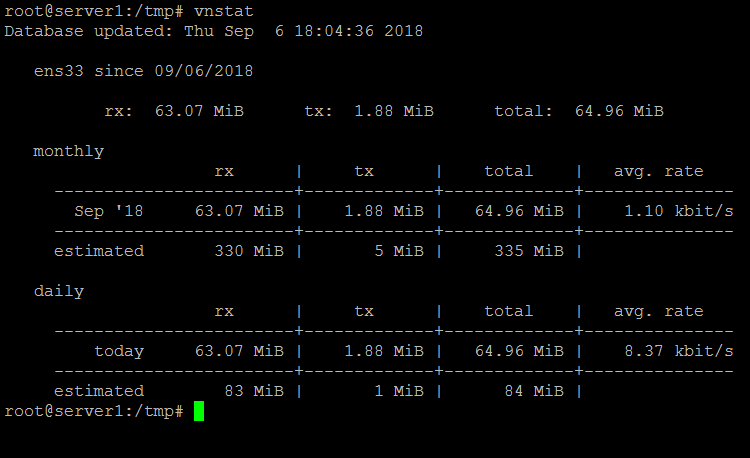
Implement network defences and monitoring software
Finally, there are some essential defences which should be in place to prevent cyberattacks and alert you to threats. These include installing a firewall, using network segmentation, a VPN (Virtual Private Network), an IDS/IPS, and updating software regularly. You can also implement network monitoring software which will provide an early warning at the slightest hint of a threat so you can act as soon as possible.