Microsoft has critical vulnerability in the Remote Desktop Protocol. So, the Burst.net send me the email about it, as below.
Recently, Microsoft published a security bulletin and recommended fix for a critical vulnerability in the Remote Desktop Protocol (CVE-2012-0002), which has the potential to impact all versions of Windows from XP through the most recent developer preview. This vulnerability allows for remote code execution by an unauthenticated attacker. More information is currently available at https://technet.microsoft.com/en-us/security/bulletin/ms12-020.
Microsoft has issued a statement confirming that CVE-2012-0002 was privately reported. This problem has been given an Exploitability Index of 1, indicating that exploit code is likely. See http://technet.microsoft.com/en-us/security/cc998259 for more details.
At this time, we are highly recommending that all clients who may be impacted by this issue:
1. IMMEDIATELY apply the provided patch.
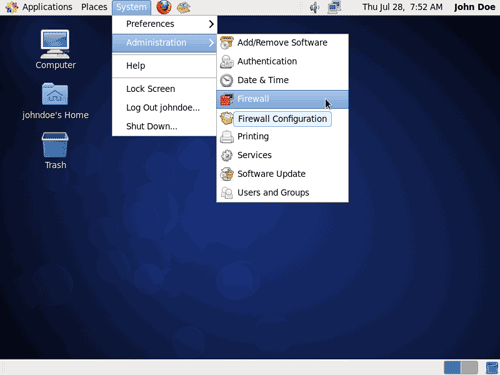
2. Enable Network Level Authentication – This will require any potential exploits to first successfully authenticate to the server before an RDP session is established.
NOTE: This RDP solution is just one of many security patches released by Microsoft this week.
Regards,
BURSTNET®
It is very important to keep your server update.
If you have a XP at home, in office, or Windows Server at data center, always setup your installation auto-update.