
How to get a perfect SSL Labs score
It is easy to get an A+ on your website. But it is a little bit hard to make a 4 parts, Certificate, Protocol Support, Key Exchange, and Cipher Strength, to be 100%. Most of time, I got A+ rating...
Tech geek. Life geek.

It is easy to get an A+ on your website. But it is a little bit hard to make a 4 parts, Certificate, Protocol Support, Key Exchange, and Cipher Strength, to be 100%. Most of time, I got A+ rating...
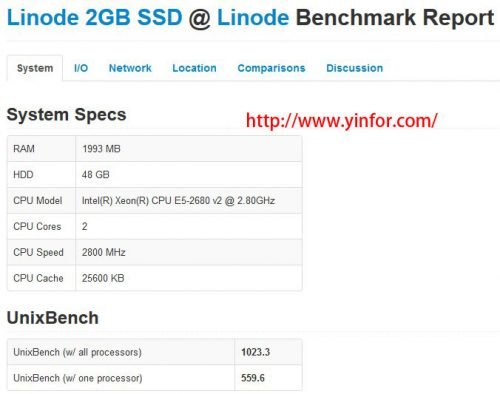
Yes, I just upgraded my VPS from old plan to new platform. Actually my old VPS at Linode is SSD cached system. They called it SSD Beta. I used it from last September. I did a performance test at that...
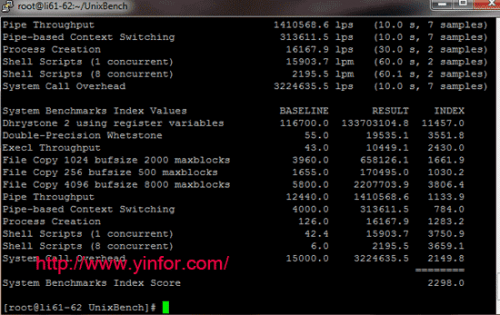
UnixBench is a testing tool. I run it on two Linode VPS. One is located at Newark, NJ, with new hardware, including CPU E5-2670. The testing results are shown as below: